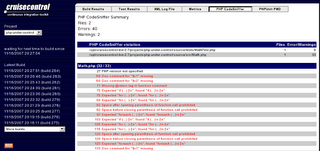
Php Tools
PHP is the commonly used open-source server-side scripting languages among all exist languages today. PHP has in depth credentials, a vast community, plenty of ready-to-use scripts and well-supported frameworks. It’s very easy to begin with PHP than with other scripting languages like Python, etc… That’s why PHP has huge community. PHP makes the development process easier and more effective with its tools and resources.
A lot of debugging and testing tools were available. Some of them were listed below.
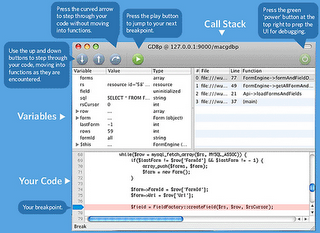
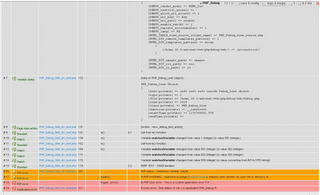
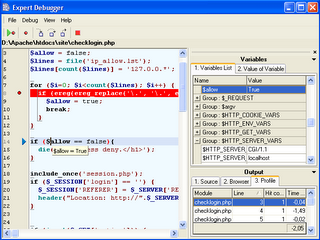
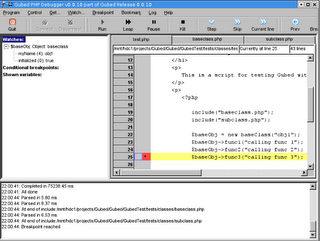
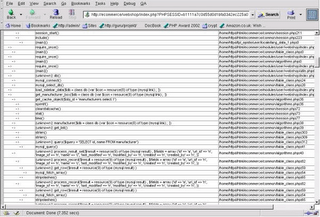
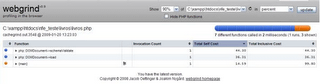
| Debugging Tools | |||||
| MacGDBp | PHP_Debug | DBG | Gubed PHP Debugger | Xdebug | Webgrind |
 |
 |
 |
 |
 |
 |
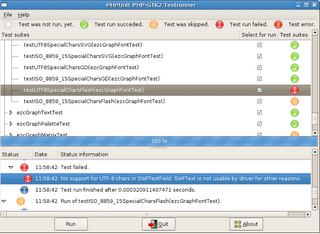
| Testing Tools | |||||
| PHPUnit | dBug | PHP_CodeSniffer | |||
 |  |  | |||
Tips to stay away from Virus
Does your system get affected by virus?
Is your files hacked by some others?
Here we have given some tips to be safe from viruses.
Operating system
The best way to improve your safety is by upgrading your system with latest version of o.s. Windows 2000 is safety when comparing to Windows 95. Linux is even better.
Email attachments
Most of the viruses were coming through mails, especially in attachments. So do not open email attachments if you are not sure about the sender.
Anti-virus software
If you are not able to locate the viruses which are hiding inside the files, it is better to run Anti-virus software. Also you should frequently update the virus recognition data file.
This software gives good protection against hackers, as it recognizes the hacking files that were trying to install on your computer.
Patches
If you need greater security, you have to apply patches. Patches are small software add-ons which are intended to deal with specific security holes and other computer problems. You can get all the patches on the Microsoft site itself.
Credit card details
While you are entering your credit card details or any other personal information on a Web site, don’t forget to check for the closed padlock or key symbol in the browser window. Only recognized sites have this logo. So if you can’t find such one, do not enter information on those sites.
Firewall
If your system is running round the clock with connecting through DSL or cable, it is essential to install firewalls. Firewalls check any program that attempt to connect with the Internet, including any hacker files on your computer. It also makes your computer invisible to Internet intruders.
File downloading
Do not download or save all the attachments in mails. Also don’t download files from all sites. You should download software from sites you trust.
Passwords
Use good passwords. Do not give names or the words you can find in a dictionary. It should be tough to predict. Also don’t keep important passwords on your machine.
File sharing
In most of the computers on Internet, file sharing is switched on. This paves the way for hackers to access all our data and information. By default, file sharing is set to “on” in computers built before 2000.You can easily change the setting.
If you take these basic safety measures, you’ve reduced your risk to the minimum and the chances of affected by viruses are extremely low.
What to do with these errors?
Errors occur while programming is common.Everyone faces errors that may be either hardware or software error.
Here We have given some funny error messages.We don’t have any idea about fixing these errors.If you are a good programmer,Tell us how to fix these errors.
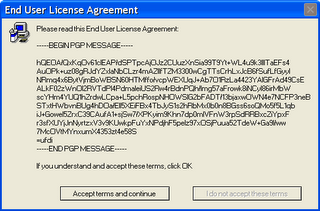
ERROR 1:
While installing an application, what you do if the user agreement is like this?
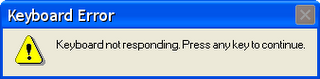
ERROR 2:
I can’t type with my keyboard.It popup an error message like below.Can anybody guide me on fixing this issue?
ERROR 3:
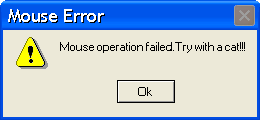
ERROR 4:
Is anybody get this kind of error? My mouse failed.What to do?
Funny Programmer
A man is smoking a cigarette and walking along on the road with his girlfriend. His girlfriend got irritated with the smoke and asked, “Did you see the warning on the cigarette pack? “. The man asked “No. What they are warning?”. The girlfriend said “Smoking is hazardous to your health!”.
To which the man replies, “I am a programmer. I don’t worry about warnings; I only worry about errors.”
Real programmers often confuse Halloween and Christmas. Do you know why?
Because dec(25) = oct(31).
Still Are you in confusion? Well, Look at this:
| DEC | = | OCT | DEC | = | OCT | DEC | = | OCT | DEC | = | OCT | |||
| 00 | 00 | 08 | 10 | 16 | 20 | 24 | 30 | |||||||
| 01 | 01 | 09 | 11 | 17 | 21 | 25 | 31 | |||||||
| 02 | 02 | 10 | 12 | 18 | 22 | |||||||||
| 03 | 03 | 11 | 13 | 19 | 23 | |||||||||
| 04 | 04 | 12 | 14 | 20 | 24 | |||||||||
| 05 | 05 | 13 | 15 | 21 | 25 | |||||||||
| 06 | 06 | 14 | 16 | 22 | 26 | |||||||||
| 07 | 07 | 15 | 17 | 23 | 27 |
The humor behind this is Halloween occurs on October 31 and Christmas occurs on December 25. When equating “oct” in October and octal, and “dec” in December and decimal, we get
DEC (25) = OCT (31)
Best Searchengines for Source Code
Are you wandering for source codes?
Did’nt get this yet?
Try in these search engines below.
We have listed the top searchengines which will provide you the exact code you are searching for.
We have listed the searchengines with respect to the traffic in Alexa.
| Google Code Search | |
 | 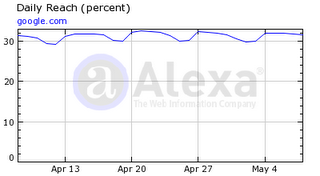 |
| Dzone | |
 | 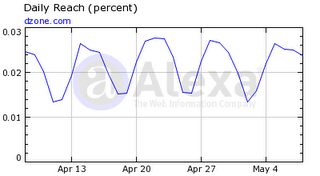 |
| Koders | |
 | 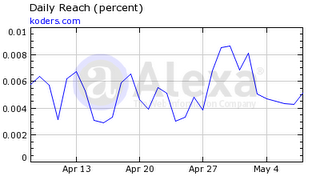 |
| O’reilly Code Search | |
 | 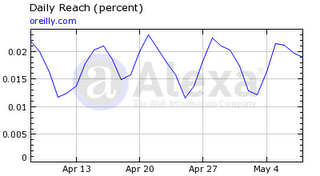 |
| Snipplr | |
 | 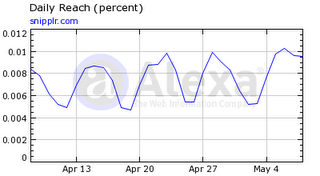 |
| Codase | |
 |  |
| Bytemycode | |
 |  |
| Krugle | |
 |  |
| Code Fetch | |
 |  |
Logos – Unknown Facts
Logos are not only meant for design.As a end user one can view the logo’s look and feel.But the designers should know the hidden meaning behind it.
View some of them here.
Can you find the symbol which is hidden in the Federal Express logo? Look at the logo. You can see the ‘arrow’ between the E and X in this logo.The arrow was to highlight swiftness and accuracy, which are part of the positioning of the company.
Paul Rand designed the iconic IBM logo in the year 1972.Later on 1981 he designed this ‘eye bee M’ logo. Actually IBM stands for “International Business Machines”.
An amazing instance of symmetry and order is the SUN Microsystems logo. When you observe the logo, the letters u and n while arranged adjacent to each other look a lot like the letter S in a perpendicular direction.
Have a look at the arrow in the logo. You may imagine that the arrow does nothing here. But it convey a message that amazon.com has everything from a to z and it also represents the smile brought to the customer’s face.
Programmers Reaction
See the reactions of an ordinary man and a programmer while in danger.
Ordinary Man
Programmer
Google introduced language option in Gmail
Do you want to send mails in tamil, hindi, malayalam or in Telugu?
Are you feel very difficult to convey your message in English?
Google now introduced language options in Gmail.
You can send mails in tamil, hindi, malayalam , Telugu and in English.
They provide suggestion for you while you are typing as they did in google suggest.
This will help you to select the exact word you want.
But they are having some drawbacks in it.
For some words, translation is wrong.
Here is a sample of error.
Even if the translation comes wrong after we hit space key, in there suggestions we cannot find the correct translation.
A sample error listing
If google fixes these minor errors, Surely this becomes very useful to the gmail users.
Not having Translator in your mailbox!!!
Here is how to enable the translation.
1. Click the Settings link in Gmail.
2. On the General tab, select the checkbox next to ‘Enable Transliteration’.
3.If there is no ‘Transliteration’ option, Then click the Show all language options link first.
4.Select the language you would like your messages to be written from the drop-down menu.
5. Save all the changes you did.
Code Injection – How and Prevention
When software permits the input of user to contain code syntax, it may be possible for a hacker to craft the code in such a way that it will change the proposed control flow of the software. Such a modification possibly will show the way to arbitrary code execution.
An injection problem covers a wide range of issues in different ways. The most significant problem to note is that each and every injection problems share one thing in common — i.e., they permit for the injection of control plane data into the user-controlled data plane. This means that the execution of the process may be misused by transferring the code through genuine data channels, using no other mechanism. While buffer overflows, and many other flaws, engage the use of some further issue to gain execution, injection problems require only for the data to be parsed. SQL injection and format string vulnerabilities are the most typical instantiations of this kind of weakness.
This illustration try to write user messages to a message file and let users to view them.
PHP Example:
[php]
$InfoFile = "seo/codeinject.out";
If ($_GET ["action"] == "Message to write")
{
$name = $_GET ["name"];
$message = $_GET ["message"];
$handle = fopen ($InfoFile, "a+");
fwrite($handle, "<strong>$name</strong> says ‘$message’\n");
Fclose ($handle);
Echo "Message Saved Successfully! \n";
}
Else if ($_GET ["action"] == "ViewMessages")
{
Include ($InfoFile);
}
[/php]
While the programmer proposes for the InfoFile to only include data, an attacker can supply a message such as:
name=h4x0rmessage=%3C?php%20system(%22/bin/ls%20-l%22);?%3E
which will decode as given below:
within php tag type the command given below
system(“/bin/ls -l”);
The programmer thought they were just including the contents of a regular data file, but PHP parsed it and executed the code. Now, this code is executed any time people view messages.
How to overcome
Your code should run in a “jail” or similar sandbox atmospheres that impose firm limitations between the process and the operating system. This may efficiently put a ceiling on code executed by your software.(Ex) Unix chroot jail and AppArmor. On the whole, managed code must be in some protected area.
Imagine all input is malicious. Use good input validation strategy. Decline any input that does not strictly conform to specifications, or transform it into something that does. Use a blacklist to reject any unexpected inputs and detect potential attacks.
To diminish the chances of code injection, use strict whitelists that set boundary which constructs are allowed. If you are dynamically constructing code that invokes a function, then verifying that the input is alphanumeric might be insufficient. An attacker can reference a dangerous function that you did not intend to allow, such as system(), exec(), or exit().